Heart-to-Heart Security Proposed for Implanted Medical Devices
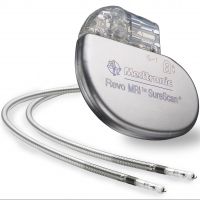
Every day, the lives of millions of people depend on wireless connections to medical devices implanted within their bodies. More than 300,000 such devices are inserted in people in the US every year. Pacemakers and Implantable Cardioverter Defibrillators are used to treat arrhythmias. For those awaiting a transplant, a Left Ventricular Assist Device helps maintain the pumping ability of a damaged heart. Insulin pumps help many diabetics maintain proper insulin levels and avoid injections.
However, like any wireless device that can be accessed remotely, this life-saving technology is vulnerable to hacking. Acknowledging that embedded medical devices can be a potential target for cyber security breaches, the FDA issued a warning to device manufacturers that they are responsible for taking steps to mitigate risks to ensure proper device performance for patient safety.
Certainly, the idea of someone tampering with a pacemaker is chilling. However, security authentication for implanted medical devices presents unique challenges, especially in emergency situations where the clock is ticking. Passwords can be lost, stolen, or forgotten. And, haven’t we all entered a password incorrectly, even when we weren’t under stress? What if a doctor or paramedic has to access a pacemaker during an emergency? Could entering passwords and authentication waste precious time?
One proposed solution under investigation—referred to as “Heart-to-Heart (H2H)”—makes use of ECG (heartbeat data) as an authentication mechanism.
MIT Technology Review reports that researchers from Rice University and the security company RSA are working on a way to match a person’s heartbeat reading to confirm that whoever is attempting to download diagnostic information or reprogram the implanted device is actually with the patient and not a remote hacker.
Using the new method, a doctor holds a device against the patient’s body, and takes a direct reading of the heartbeat. The device reads the patient’s heartbeat and compares it to one relayed in a wireless signal from the implant, and then confirms that the signals match. The wireless exchange of the heartbeat signal is encrypted, thwarting any attempt to hijack the communications during the exchange.
The H2H solution is years away from commercial implementation, but it opens up intriguing possibilities. After all, hacking someone’s financial information is terrible, but hacking a heart device could be fatal.

